Security System with Access Control System
When considering your premises’ safety & security, it is vital to get a system that can provide protection via the premises effectively. In business organizations where professionalism is only needed factor there from your reception up to your lobby, everything should be protected by security systems so that individuals visiting your premises can relax in terms of your safety needs. How will you judge a good security system? But, the obvious thing is that one will not go on looks. Based on the look of the device the security systems for your premises can never be decided. Consequently, what can be your selection criteria? Possibly, there are selection criteria that can be based on affordability, reliability, & efficiency. Thus, one needs to go for the security device that meets your criterion. To get a cost-effective, reliable & efficient security device is now not a problem to achieve with a visitor access control system.
When it comes to safety you need to be very conscious about yourself & very particular about selecting safety devices. It is not only about safety but if you are in the organizational sector then it becomes somehow very vital to create your first impression. As there is a general fact is the first impression is your last impression, thus creating your first impression in front of your clientele is vital. The electronic visitor management system looks absolutely well-designed in your premises not only it gives your premises a fascinating impression of campus but also endures perfect security.
What is Visitor Management System?
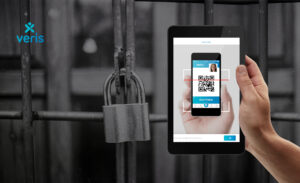
These are the tools like Veris Visitor Management System which help your premises create & execute their visitor management policies. Nowadays, organizations understand the importance of a visitor management system. Many are upgrading from the traditional pen & sign-in book to a digitized system that effectively records who is getting in and out of the building.
Technology behind the Visitor Access Control System
Apart from its looks & features, the most vital is modern technology on which it is based. The visitor management system is based on face recognition technology. The face identification system works by capturing the facial details of people on the premises. The facial details are then stored inside the database of your computer. When the individual re-visits your premises then the facial identification system again captures facial details & then it performs the matching procedures by using the matching algorithm between older & newest captured patterns. When the visitor management system finds the match, it grants the authentication else it denies the authentication. Depending upon the procedure security is maintained at your premises. With a visitor iPad check-in system, one can even set lower priority individuals, so, they can be strictly prohibited from a particular area.
Importance of Smart Visitor Sign-in Software
Welcoming guests to your premises is the backbone of a successful business. From large companies to schools & hospitals, visitors play an important role in all industries. Though, controlling your guests is essential for ensuring minimum employee disruption & creating a positive visitor experience. Below are the benefits of visitor check-in software –
Improve access control & site security
A formal visitor check-in system & the designated point of your premises’ entry/exit work hand in hand with access control to improve the security of the overall premises. You have to invest in the smart visitor management software that issues your personalized & dated visitor pass shows your premises takes security seriously. When teamed with the ID badges it becomes an easy way to spot the intruder, mainly if staff is educated which safety is the responsibility and it is not impolite to challenge anyone who does not display the valid badge.
Beef-up your Organization
It is also the chance to boost your brand identity by simply including your logos & color schemes in visitor pass design & welcome check-in screens to help you to create a strong and consistent image of your organization. The visitor sign-in system itself should be the credit to your organization. A paper visitor pass book should be well-presented, robust, & durable enough for frequent use & a visitor touchscreen should be intended for continual operation in demanding situations.
Help your busy admin team
Whether you are exploring for the visitor book or visitor touchscreen system, both systems streamline your signing-in process & taking pressure off your busy receptionist & security guard. You do not want the reception to develop a bottleneck where the attending staff of your organization are too rushed and make your visitors feel welcome with a special greeting. Both the systems give visitors a uniform set of information to complete and hence regulating your data capture procedure.
Analyze and review your visitor’s logbooks in the real-time
Organizations can analyze & review your visitor data anytime, all thanks to the cloud integrations & virtual dashboards which enable real-time data reports. Further, all such reports help you to review your whole visitor operations & help in making the data-backed decisions to boost the overall productivity of your organization.
Create your historic records
Do you know how many guests are on your premises right now? How about yesterday? How about 7th September 2017? There are numerous situations where your company or organization might need accurate historic records of who was on your premises over the specific time period. For instance, the food processing plant might need to identify contamination sources, or the organization might want to examine the safeguarding issue.
Schedule the approved visitors
The effective visitor management system will allow your staff to schedule the approved visitors. It will help to eliminate the unexpected arrivals & departures of visitors, thus receptionists & facility management know who to expect & when. Since the visitors are pre-registered automatically, visitor check-in software also helps to increase the productivity of your reception area & allows multiple visitors to be processed instantaneously.
Optimize the visitor management procedure
Visitor access control software is meeting & resource booking software available for Microsoft Outlook® & exchange that allows you to identify, log, & report on visitors for your facility. The software maximizes the efficiency of your front desk & reduces your receptionists’ workload by allowing the visitors to sign in or sign out themselves and quickly receive visitor badges. Using the software frees receptionists up & allows them to work on various other important projects of your organization.
Improves your employee’s productivity
The visitor access control software is not restricted to just your premises visitors. Employees can simply check to your building without worrying about contracting the virus. Older visitor management solutions required the employees to touch the fingerprint scanner for the system to identify their unique fingerprint ID. But, with the facial & touchless visitor recognition systems in place, the human touch is the thing of the past. Employees can protect themselves, save their time, organize their tasks effectively, and hence enhance your organization’s productivity.
Bottom-line
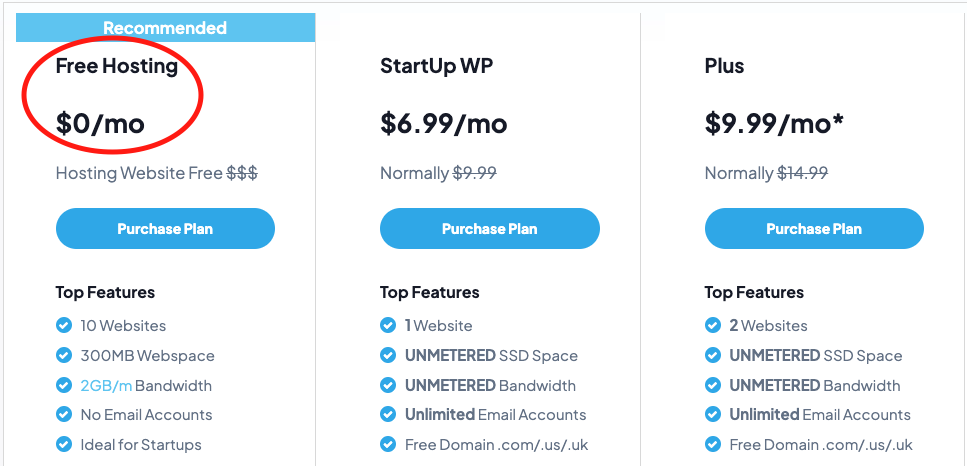
Starting a security system consulting business can be a profitable venture. With the increasing demand for security solutions, there is a growing need for experienced security consultants who can help businesses and individuals assess their security risks and recommend solutions. In this article, we will discuss the steps involved in starting a security system consulting business using an online website from Bluehill Hosting.
Step 1: Conduct Market Research
The first step in starting a security system consulting business is to conduct market research. You should identify your target market and understand their security needs. You may choose to focus on a specific industry, such as healthcare or finance, or offer a range of security solutions to businesses and individuals. You should also research your competition and understand their pricing and services.
Step 2: Create a Business Plan
Once you have conducted market research, you will need to create a business plan. Your business plan should outline your goals, target market, services, pricing, marketing strategy, and financial projections. You may also need to obtain any necessary licenses and permits to operate your business.
Step 3: Choose Your Website Platform
The next step is to choose a website platform to host your online website. Bluehill Hosting offers a range of website hosting solutions that can support your security system consulting business. You should choose a website platform that is user-friendly, customizable, and secure. You will also need to purchase a domain name and hosting for your website.
Step 4: Develop Your Website Content
Once you have chosen your website platform, you will need to develop your website content. Your website should include information about your security consulting services, your experience and qualifications, and any relevant certifications. You may also want to include customer testimonials and case studies to demonstrate your expertise.
Step 5: Create a Marketing Plan
To promote your security system consulting business, you will need to create a marketing plan. You should identify your target audience and develop marketing messages that resonate with them. You may choose to use social media, email marketing, and paid advertising to reach your target audience. You should also consider attending industry conferences and networking events to build relationships with potential clients.
Step 6: Develop Your Consulting Process
As a security system consultant, you will need to develop a consulting process that you can use with clients. Your consulting process should include an initial assessment of the client’s security needs, the development of a security plan, and the implementation of security solutions. You may also provide ongoing security monitoring and support to clients.
Step 7: Set Your Pricing
You will need to set your pricing for your security system consulting services. You may choose to charge hourly rates, project-based fees, or a retainer for ongoing consulting services. Your pricing should reflect your level of expertise and the value you provide to clients. You may also want to offer discounts for referrals or bulk services.
Step 8: Build Relationships with Clients
To build a successful security system consulting business, you will need to build strong relationships with clients. You should listen to their security concerns and provide solutions that meet their needs. You may also want to provide ongoing support and monitoring to ensure their security solutions remain effective.
Step 9: Continuously Improve Your Services
As your business grows, it is important to continuously improve your services. You should stay up-to-date on the latest security threats and solutions and invest in training and certifications to enhance your skills. You should also seek feedback from clients and make improvements to your consulting process and services based on their feedback.
In conclusion, starting a security system consulting business using an online website from Bluehill Hosting requires careful planning, market research, and a strong commitment to customer service. By following these steps, you can build a successful business that helps businesses and individuals protect their assets and maintain their security.
- https://www.getveris.com/
-
Visitor-Management-security - on